Why symmetric Encryption Matters
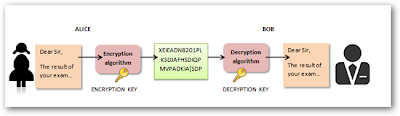
Symmetric encryption is a vital tool in cybersecurity, as we noted in our discussion on IS security and risk management, where encryption was highlighted as a key control for protecting data. Here’s why it’s so important:
1. Speed and Efficiency
Symmetric encryption is significantly faster than asymmetric encryption because it uses simpler mathematical operations. This makes it ideal for encrypting large volumes of data, such as entire databases or real-time communications.
2. Strong Security with Modern Algorithms
Modern symmetric algorithms like AES and ChaCha are highly secure when paired with sufficiently long keys (e.g., 256 bits). AES, adopted as a standard by NIST in 2001, is trusted by governments and industries worldwide to protect classified information.
- Impact: It’s a reliable choice for securing sensitive data, from financial records to medical files.
3. Foundation for Everyday Security
Symmetric encryption underpins many technologies we use daily:
- Disk Encryption: Tools like BitLocker use AES to encrypt entire hard drives.
- VPNs: Symmetric encryption secures data transmitted over virtual private networks.
- Messaging Apps: Apps like WhatsApp use AES to encrypt messages end-to-end.
- Impact: It ensures privacy and security for billions of users.
Benefits of Symmetric Encryption
- Performance: Faster than asymmetric encryption, ideal for large datasets or real-time applications.
- Simplicity: Uses a single key, reducing computational overhead.
- Strong Security: Modern algorithms like AES are resistant to brute-force attacks with proper key lengths.
- Versatility: Suitable for a wide range of applications, from file encryption to secure communication.
Challenges of Symmetric Encryption
While powerful, symmetric encryption has limitations:
- Key Distribution: Securely sharing the secret key between parties is a major challenge, especially over the internet. If the key is intercepted, the encryption is compromised.
- Solution: Use asymmetric encryption to securely exchange the symmetric key, a common practice in hybrid systems like SSL/TLS, as we discussed in the asymmetric encryption article.
- Scalability: Managing keys for large groups is complex—each pair of users needs a unique key, leading to a key management nightmare as the number of users grows.
- Solution: Implement a key management system (e.g., AWS KMS) to securely store and distribute keys.
- No Authentication: Symmetric encryption doesn’t inherently verify the sender’s identity, making it vulnerable to impersonation.
- Solution: Combine with digital signatures or use protocols that include authentication.
Real-World Applications of Symmetric Encryption
Symmetric encryption is widely used to secure our digital lives:
- End-to-End Messaging: WhatsApp and Signal use AES to encrypt messages, ensuring only the recipient can read them.
- Cloud Storage: Services like Google Drive use AES-256 to encrypt files at rest, protecting user data.
- Payment Systems: Symmetric encryption secures credit card transactions during processing, adhering to PCI DSS standards.
- IoT Devices: Smart home devices use symmetric encryption to secure communication between devices.
Symmetric Encryption in Action: An Idecademian’s Use Case
Consider an Idecademian—a member of the alumni community we’ve discussed—who runs a healthcare startup. To comply with HIPAA regulations, they use AES-256 to encrypt patient records stored in the cloud, ensuring confidentiality. They also use symmetric encryption in their app to secure real-time communication between doctors and patients, leveraging its speed for seamless performance. By implementing a key management system, they address the challenge of securely sharing keys among their team, demonstrating how symmetric encryption protects sensitive data while supporting operational efficiency.
Symmetric vs. Asymmetric Encryption: A Quick Comparison
Since we recently explored asymmetric encryption, let’s compare the two:
- Key Usage: Symmetric uses one key; asymmetric uses a public-private key pair.
- Speed: Symmetric is faster, ideal for large data; asymmetric is slower but better for key exchange.
- Use Case: Symmetric excels in bulk encryption (e.g., file storage); asymmetric is key for secure key exchange and authentication (e.g., SSL/TLS).
- Hybrid Approach: Many systems, like HTTPS, use asymmetric encryption to share a symmetric key, combining the strengths of both.
The Future of Symmetric Encryption
Symmetric encryption will remain relevant but evolve:
- Quantum Resistance: While AES-256 is considered quantum-resistant with longer keys, new algorithms may emerge to counter quantum threats.
- AI Optimization: AI will enhance key generation and management, reducing human error.
- IoT Growth: Symmetric encryption will play a larger role in securing the expanding IoT ecosystem, requiring lightweight algorithms like ChaCha for resource-constrained devices.
Conclusion
Symmetric encryption, with its single-key approach, is a fast, efficient, and secure method for protecting data, making it a vital tool in cybersecurity landscape. From encrypting cloud storage to securing messaging apps, its applications are vast, as we noted in our discussions on IS security and risk management. While it faces challenges like key distribution, solutions like hybrid encryption and key management systems make it practical for modern use.
Whether you’re an Idecademian securing a digital venture or a business protecting customer data, symmetric encryption offers a reliable foundation. Ready to implement it? Explore tools like OpenSSL for AES encryption or check your cloud provider’s encryption options, and start safeguarding your data today.
No comments:
Post a Comment